- Compare Editions
- Product Information
- Resources
- Licensing / Pricing
- Support
- Contact
Back to Setup Guide for Ransomware Protection
Some customers have come up with their own mitigation techniques during a ransomware attack. These might involve removing user rights from directories, forcing a logout of a user account, etc.
To run an external program as an action in response to the monitor detecting active ransomware activity, use the Start Application action.
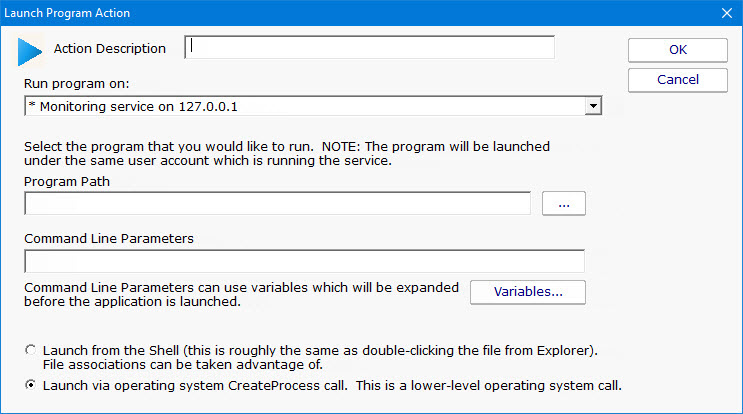
IMPORTANT: When setting up the Start Application action it is important to pay attention to where the application/program is going to be run. This is shown near the top of the action configuration dialog.
“I keep forgetting how easy you make this software. I love Power Admin. Great product at a very fair price!!”
Erik M., The Milton Bank, USA