- Compare Editions
- Product Information
- Resources
- Licensing / Pricing
- Support
- Contact
Back to Setup Guide for Ransomware Protection
Most ransomware attacks will either leave a ransom note in the folders they attack, or they will rename the encrypted files with a new extension. For example, finance.xls might become finance.xls.encrypted after it has been encrypted.
There are a number of sites on the Internet that keep lists of file extensions and ransom note filenames that have been seen. PA File Sight can watch for these being written. The danger of course is any malware writer can change their malware to use different extensions and ransom note filenames. Similar to the honey pots method, this is a simple method that is simple to setup so it doesn't hurt to add it.
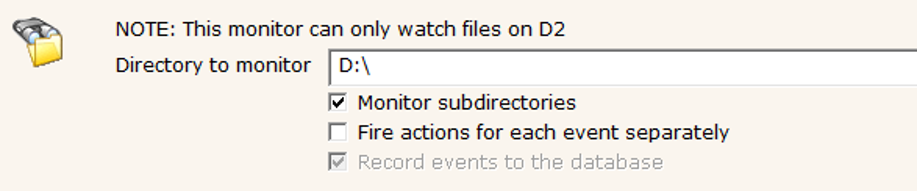
Create a new File Sight monitor to watch the target folder D:\
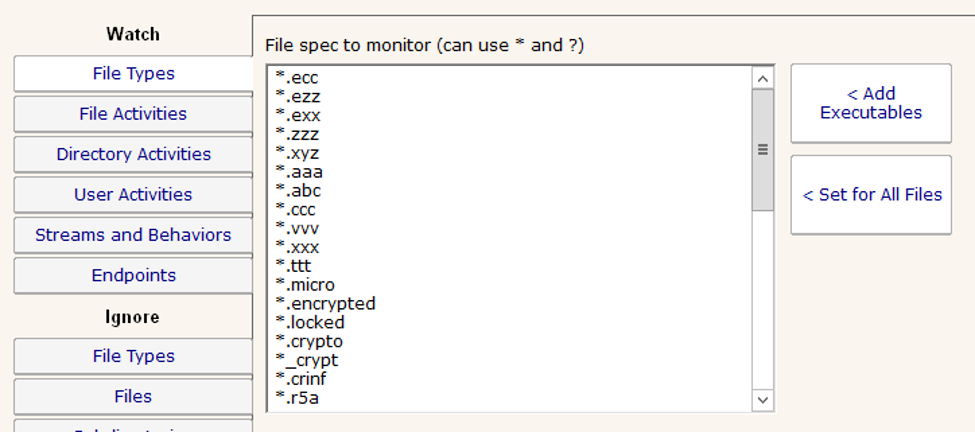
Get a list of typical encrypted file extensions. There are a variety of lists on the Internet with these lists. One example is https://fsrm.experiant.ca/ (scroll down to "Raw List").
These lists will always be outdated, but find the newest one you can to protect against the latest known ransomware variants.
On the File Types tab, you can replace the * and insert the list of file extensions you found. They need to be in the format of:
Double check the list to make sure there aren't any file extensions that might be typically used at your location, and if there are, remove them.
You can also paste a list of ransom note filenames that are in the format of:
as shown below:
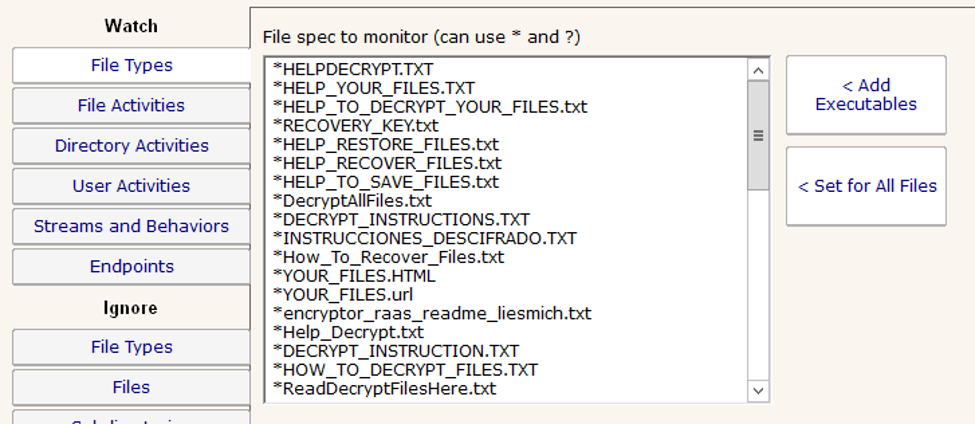
Be VERY careful and check this list of files carefully. Readme.txt is often included in these lists, but it is also a popular and legitimate filename.
Note that filenames and extensions are NOT case sensitive.
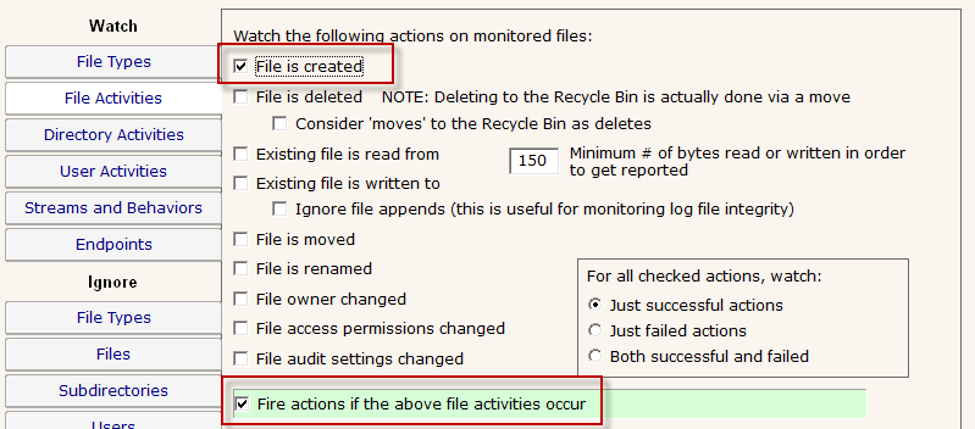
For the File Activities tab, we want to be alerted if a file is created that has one of the target extensions:
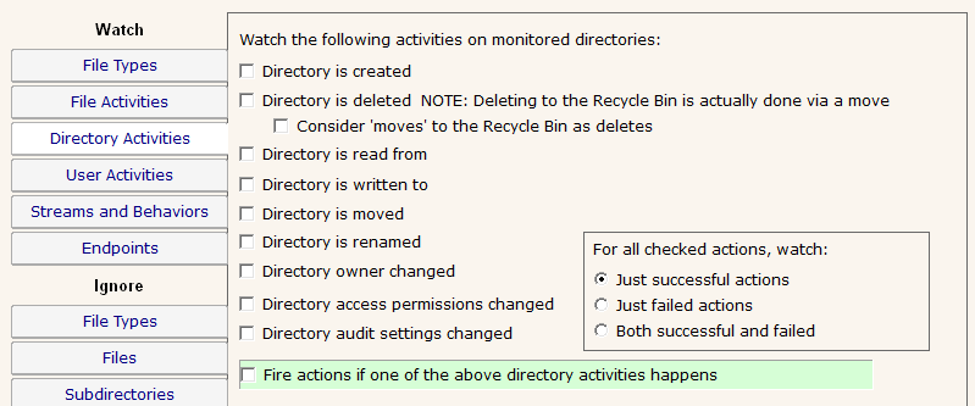
Uncheck everything on the Directory Activities tab:
For this monitor, there isn't much reason to ignore anything. The rest of the tabs can be skipped.
“[ PA Server Monitor's benefit is less] wasted labor in tracking what was unbillable - that now ADDS a LOT more BILLABLE time addressing issues we just could not get to before - making networks we manage much more stable and reliable. WE do a BETTER job for our clients and capture time we basically 'gave away' before.”
Oly G., On-Site Computer Solutions, USA