 When planning a BitLocker deployment in your Windows Infrastructure, you’ll need to take into consideration many factors that can/will influence your network. This technology was first released with Windows Vista and introduced two important security features: encryption of hard drives and integrity check for data. This means that if a device was stolen, no data could be recovered from it since everything is encrypted. With BitLocker, not only is the OS encrypted, but also data, page file, applications and application configuration. There are several methods with which you can access encrypted information from a volume protected with BitLocker. One solution is to use a pre-configured key that grants access to the data. One big problem of using such keys is the fact that if those are lost, the entire system becomes untouchable and all data is lost.
When planning a BitLocker deployment in your Windows Infrastructure, you’ll need to take into consideration many factors that can/will influence your network. This technology was first released with Windows Vista and introduced two important security features: encryption of hard drives and integrity check for data. This means that if a device was stolen, no data could be recovered from it since everything is encrypted. With BitLocker, not only is the OS encrypted, but also data, page file, applications and application configuration. There are several methods with which you can access encrypted information from a volume protected with BitLocker. One solution is to use a pre-configured key that grants access to the data. One big problem of using such keys is the fact that if those are lost, the entire system becomes untouchable and all data is lost.
BitLocker is a feature included in different Windows Server 2008 editions![]() and you can add it using the Server Manager console. Note that one important requirement of BitLocker is the TPM (Trusted Platform Module) chip and a BIOS that supports it. These two components are needed when performing data integrity checks. With TPM, BitLocker verifies the startup information (Boot Sector, Windows Loader, BIOS, MBR and Boot Manager) of the Operating System and if some altered data is discovered, the volumes become locked and data cannot be accessed. This means that you will need to unlock the System using a BitLocker key. One problem for System Administrators is when there is any maintenance on the BIOS level, because BitLocker locks the drives with every reboot. So you may end up recovering the System because the drive becomes unavailable.
and you can add it using the Server Manager console. Note that one important requirement of BitLocker is the TPM (Trusted Platform Module) chip and a BIOS that supports it. These two components are needed when performing data integrity checks. With TPM, BitLocker verifies the startup information (Boot Sector, Windows Loader, BIOS, MBR and Boot Manager) of the Operating System and if some altered data is discovered, the volumes become locked and data cannot be accessed. This means that you will need to unlock the System using a BitLocker key. One problem for System Administrators is when there is any maintenance on the BIOS level, because BitLocker locks the drives with every reboot. So you may end up recovering the System because the drive becomes unavailable.
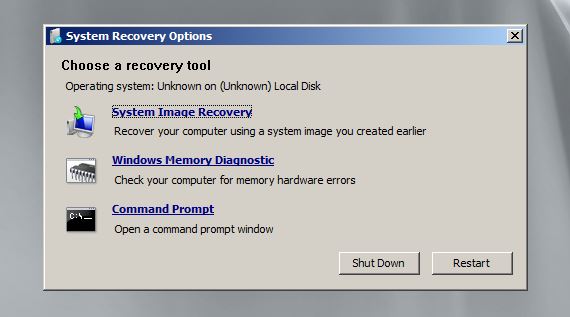
To configure BitLocker you will need to partition your hard drive correctly. You must first create an extra partition that is around 2 GB that’s marked as active and will be used by BitLocker. Once you’ve created this partition you can add more primary partitions but make sure there is plenty of space for the OS. To create a partition and mark it as active you will need to boot from the installation media in Recovery mode. If you’re using a virtual machine in VMware, you will need to disable Easy Install and then boot in the installation media. At the installation page, select Repair your computer and click Next until you reach the System Recovery Options and open a Command Prompt:
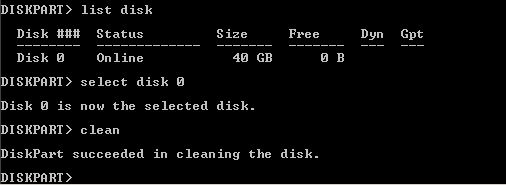
For this operation we will use Diskpart which is a partitioning tool provided by the OS. We will need to create at least two partitions, one for BitLocker and the other one for the OS, by typing the following commands:
List Disk
Select Disk 0
Clean
With these commands we have listed the available disks and we’ve selected the one that will be partitioned. Because my VM has only one disk, I’ve selected it by using its Disk ID (0). The clean command has been executed to empty the whole disk:
Now it’s time to create the two partitions by executing the following commands:
Create partition primary size =38000 – the C partition in which the OS will be installed
Assign letter C
Create partition primary size 2000 – The BitLocker partition
Assign letter R
Active – we’ve marked this partition as active
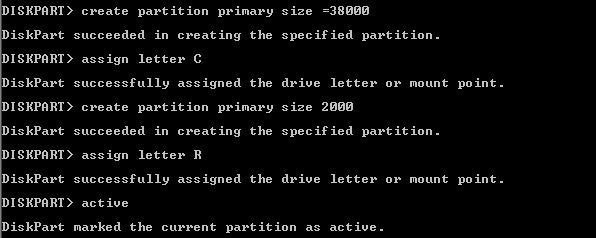
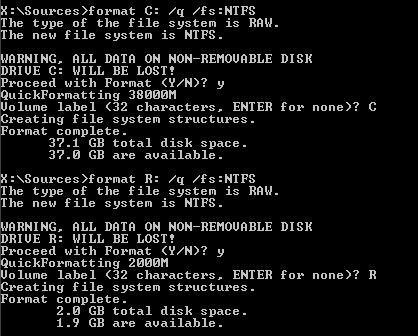
You can now execute list partition command to verify if the partitions were created successfully. We’ve created the partitions and it’s time to format them as assigned a file system. Type exit to return to CMD and execute the following commands:
Format C: /q /fs:NTFS
Format R: /q /fs:NTFS
/q – performs a quick format /fs – used for selecting the file system, in this case NTFS
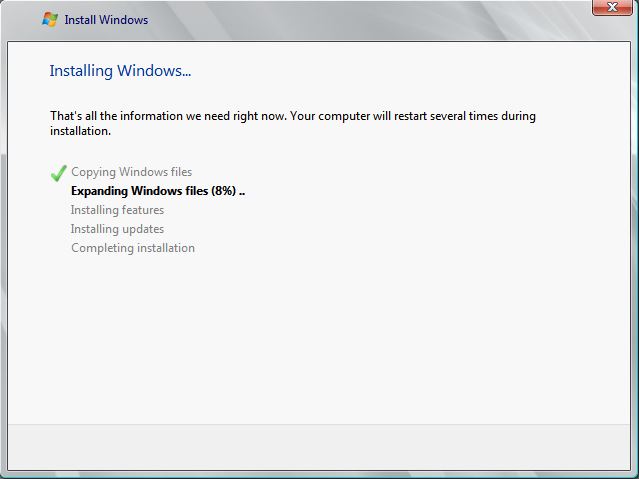
Now close Command Prompt and exit the Recovery console then click Install Now. Note that you will need to select the secondary partition (C) as the installation drive for the OS. Be patient because the install operation takes a long period of time:
Navigate to local group policy to view the available BitLocker policies. My VM does not support TPM chip, so I will have to enable a policy that will bypass this missing component. Note that not all devices have a TPM chip included so if this is your case, you’ll need to configure the Server to be unlocked using a startup password.
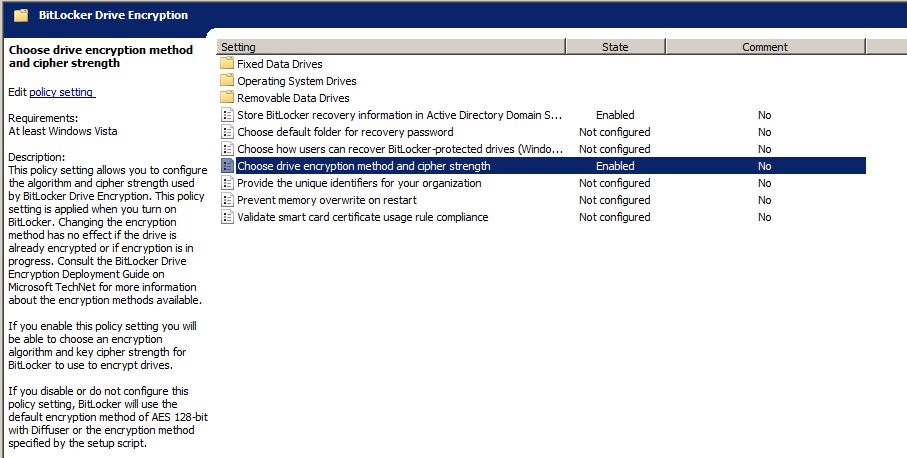
Once you’ve opened the console, navigate to Computer Configuration\Administrative Templates\Windows Components\BitLocker Drive Encryption and view the available group policies:
In group policy, navigate to Operating System Drives and double click on Require additional authentication at startup (Windows Server 2008 and Windows Vista) policy and Enable it:
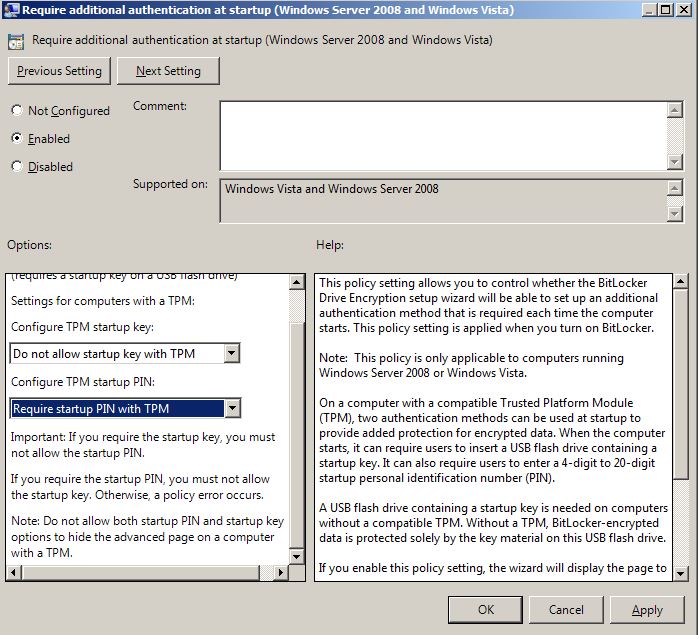
I will not allow the startup key with TPM because I do not have such chip but, I will require startup PIN with TPM.
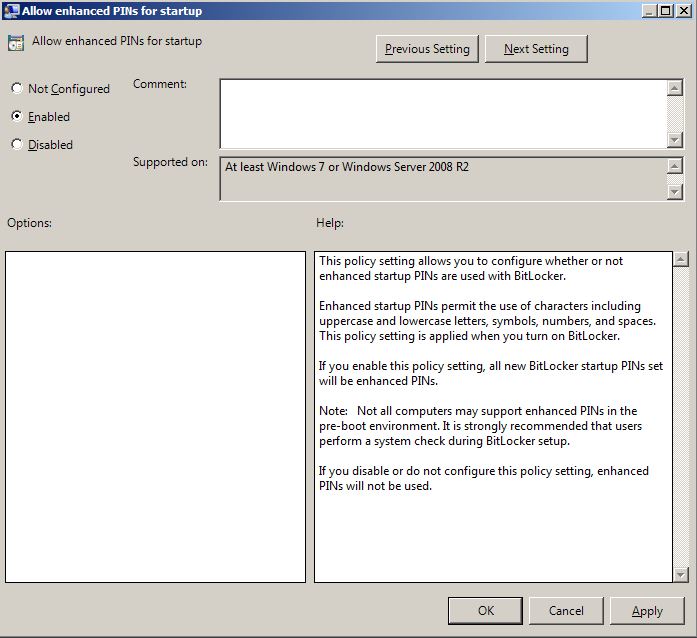
Click on the Next Setting button and enable enhanced PIN for startup. This policy will allow complex unlock passwords that can use uppercase letters, lowercase letters, numbers, symbols and spaces.
In the next policy we will set a minimum password length of 8 characters:
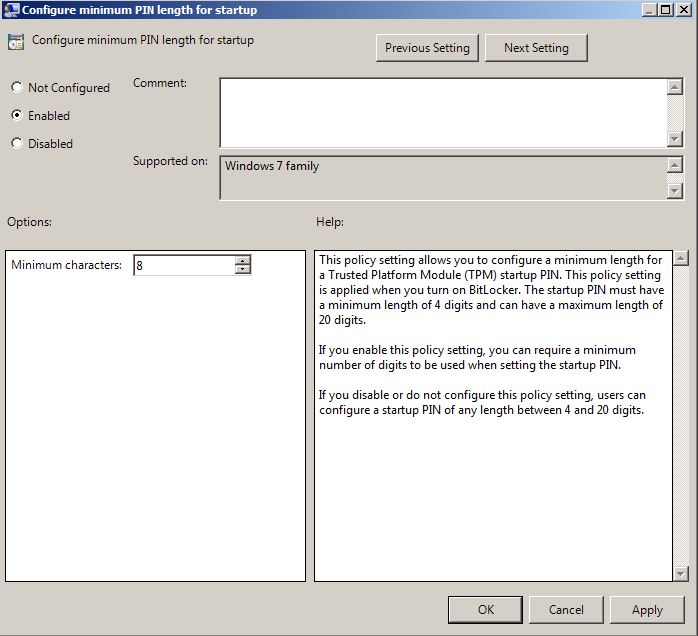
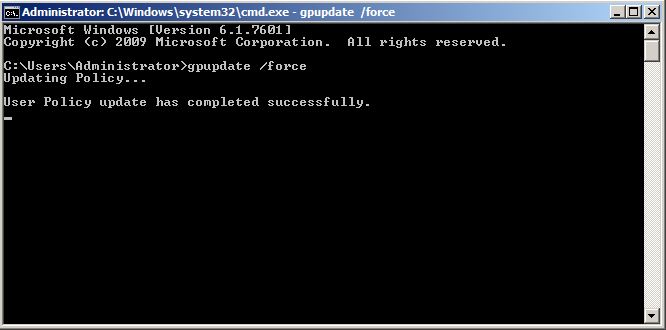
After you’ve enabled all these policies you’ll need to execute gpupdate /force from Command Prompt to update the server with the latest policies:
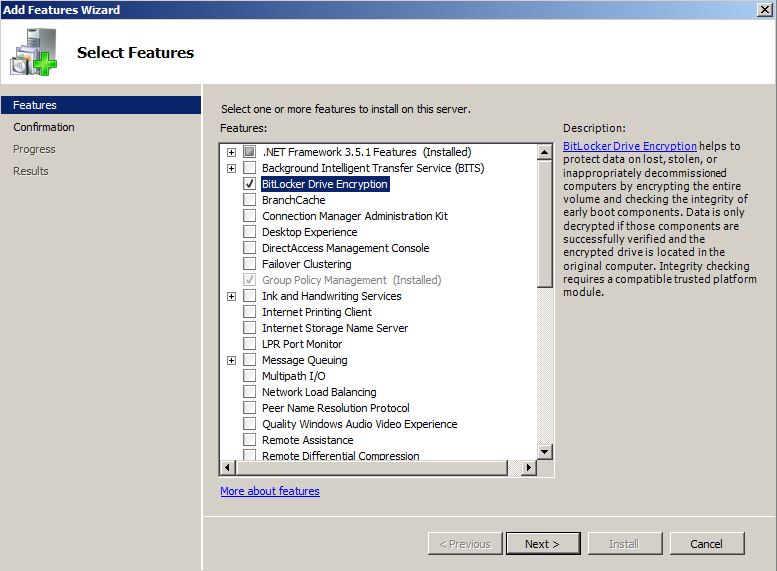
Open Server Manager Console, navigate to the Features section and add click on Add Features. From the features list select BitLocker Drive Encryption and wait for the installation to finish. When the installation is completed, the server will require a reboot.
We will enable BitLocker Drive Encryption on our C partition. Open Control Panel and navigate to \System and Security\BitLocker Drive Encryption and click on Turn on BitLocker:
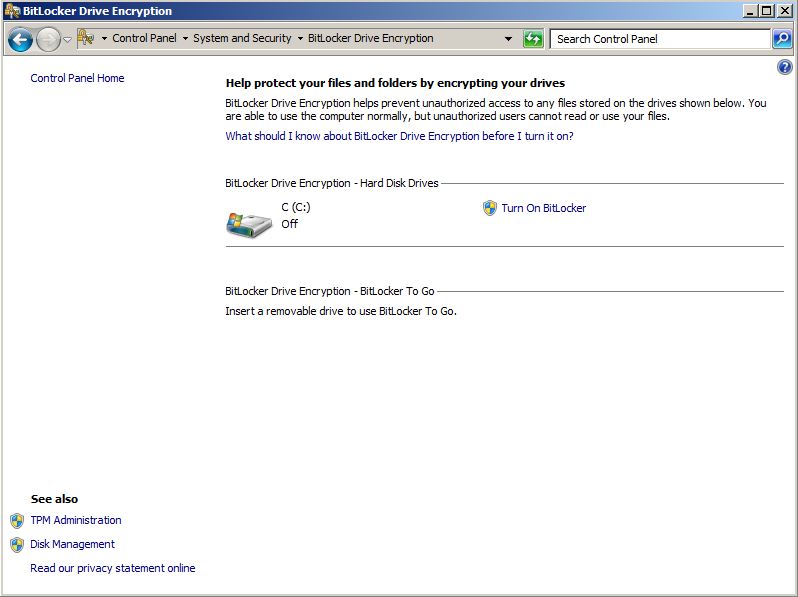
Note that the whole BitLocker operation will take a long period of time (from one to several hours) so you can do other things in the meantime. Follow the BitLocker Wizard and prepare a USB drive on which you’ll save the BitLocker Recovery Key. Once the encryption is completed, a reboot will be necessary. With all these things configured, you’ll now have a Windows Server 2008 protected with BitLocker.
After reading this article I hope you will be able to configure BitLocker on your Windows Server without encountering too many problems. For any misunderstandings, don’t hesitate to post a comment in our dedicated section and I will respond as soon as possible. Wish you all the best and stay tuned for the following articles.


