- Solutions
-
- File Server: Ransomware Protection
- File Server: File Copy
- File Server: Audit File Access
- File Server: Storage growth reporting
- Licensing/Pricing
- Contact
This help page is for version 8.2. The latest available help is for version 9.4.
The Active Directory Login Monitor watches the Security Event Log and records logins to a database. It can also alert for certain login events, and run reports later to see a history of logins.
The monitor is powerful, yet simple to setup. All events get written to the database so you have full reporting capability later. To alert on specific events, check the box next to the category.
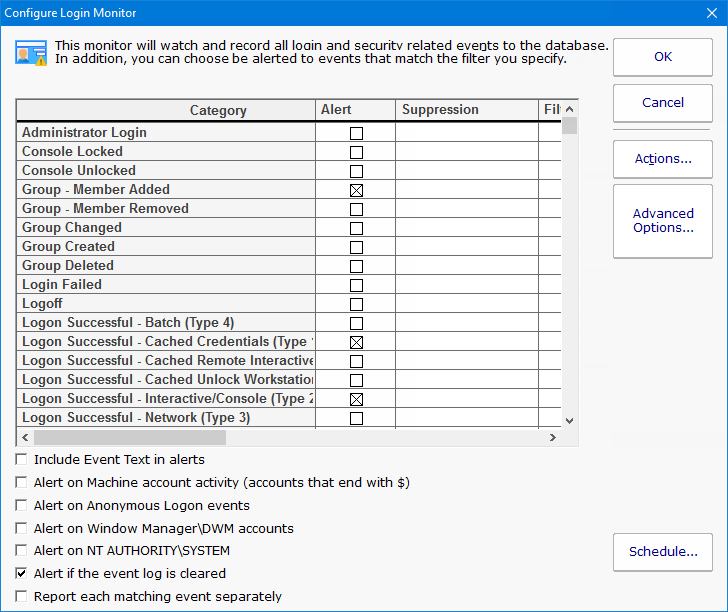
There are many types of logins and similar events that the monitor will watch. These events are grouped into the following categories:
In addition to login tracking, there are other events that are tracked that involve security, such as user and group changes, accounts and consoles locked, etc.
|
|
There are some events, such as failed login attempts, that you only care about if there are a lot of them in a short amount of time (indicating some sort of break in attempt). The Suppression setting lets you configure a threshold for how many have to happen before an alert is fired.
If there are specific accounts, workstations, etc, that you don't want to be alerted about, you can exclude them, or only include specific targets. The filter text is checked against the entire Event Log Event text, so it can target any part of the event.
To see specifically which Event IDs are included in each category, scroll to the right and there is Definition column. Hover the mouse over any row to see the Event IDs in that category.
Windows has many types of logins, including:
By default, the non-normal login types are ignored, but you can choose to alert on them if they are of a category that is being monitored.
There are a few different types of reports available that make it easy to find out what login activity happened.
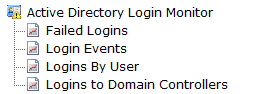
The Login Events report is especially flexible with many options for selecting the events you want to see, as shown below.
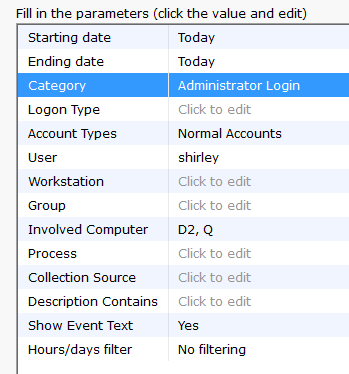
Not all fields make sense for all event types. So you would just fill in the details you care about and let the report find the appropriate events for you.
Like all monitors, this monitor has standard buttons on the right for Adding Actions, setting Advanced Options and setting the Monitor Schedule.