This help page is for version 9.2. The latest available help is for version 9.4.
Trusted Application (Application Whitelisting) Statements
Each time a file is accessed, data about the file and also about the process accessing the file is made available to
Trusted Application Rules. The rules are evaluated and access to the file is either allowed or denied based on the outcome
of the evaluation. Rules are made up of logical checks against Statements.
Each statement below evaluates to True or False, or to a string value for the file access that is being checked. Comparisons (such as
comparing a value to a string) are case insensitive. You can read more about each statement below.
Note that file extensions don't guarantee the type of file but serve as a hint in most cases. Trusting them is not always safe.
- FILE_COPY_SOURCE
- If IS_PROBABLE_COPY is True, then this is the path of the source file of the copy.
- FILE_EXTENSION
- Evaluates to a string containing the file extension including dot. Example: (FILE_EXTENSION = ".exe")
- FILE_HAS_EXECUTABLE_EXTENSION
- Evaluates to True or False. The file's extension is checked against the Executable Extensions list, and if found, the statement
evaluates to True, otherwise to False. FILE_IS_EXECUTABLE or FILE_IS_DLL are more reliable checks, though they takes longer to check. Example: (FILE_HAS_EXECUTABLE_EXTENSION = True)
- FILE_HAS_EXECUTABLE_OR_SCRIPT_EXTENSION
- Evaluates to True or False. The file's extension is checked against the Executable Extensions list and the Script Extensions list,
and if found in either, the statement evaluates to True, otherwise to False. Note that trusting file extensions is not always safe. Example: (FILE_HAS_EXECUTABLE_OR_SCRIPT_EXTENSION = False)
- FILE_HAS_TEXT_EXTENSION
- Evaluates to True or False, based on whether the file's extension is found in the Text Extensions list. Example: (FILE_HAS_TEXT_EXTENSION = True)
- FILE_IS_COMMAND_HOST
- Evaluates to True or False, depending on whether the file name (excluding path) is found in the Command Hosts list. If CMD.EXE was in the
Command Hosts list, both C:\cmd.exe and C:\Windows\System\cmd.exe would evaluate to True. Example: (FILE_IS_COMMAND_HOST = False)
- FILE_IS_DLL
- Evaluates to True or False, depending on whether the file is an DLL file based on a check of the file header. This is slower, but more trustworthy than
the FILE_HAS_EXECUTABLE_EXTENSION check because the file header is checked. Typically .DLL, .CPL, .OCX, etc files will meet the criteria. Example: (FILE_IS_DLL = True)
- FILE_IS_EXECUTABLE
- Evaluates to True or False, depending on whether the file is an executable file based on a check of the file header. This is slower, but more trustworthy than
the FILE_HAS_EXECUTABLE_EXTENSION check. Typically only .EXE files will meet the criteria. Example: (FILE_IS_EXECUTABLE = True)
- FILE_PATH_IS_REMOTE
- Boolean indicating if the file path is on a remote computer, such as with a mapped drive or UNC path. Example: (FILE_PATH_IS_REMOTE = False)
- FILE_IS_SIGNED
- Evaluates to True or False. The file is checked for a digital signature, and if found, the result is True. Example: (FILE_IS_SIGNED = True)
- FILE_IS_TEXT_FILE
- Evaluates to True or False. The file is opened and inspected using heuristics on the first 64KB to determine whether it appears to be a text file or not.
Example: (FILE_IS_TEXT_FILE = True)
- FILE_PATH
- Evaluates to a string containing the full path of the file being accessed. Example: (FILE_PATH = "C:\Users\Bob\Documents\Bob's Updates.docx")
- FILE_PATH_IN_CLOUD_FOLDER
- Evaluates to True or False indicating if the file is located within a local cloud product folder. OneDrive, Google Drive and DropBox are currently detected and supported. Example: (FILE_PATH_IN_CLOUD_FOLDER = True)
- FILE_PATH_IN_EXTERNAL_DRIVE
- Evaluates to True or False indicating if the file is located on an external drive, such as a USB thumb drive. Example: (FILE_PATH_IN_EXTERNAL_DRIVE = True)
For the FILE_RENAME_DEST_xxx statements below, IF the file operation is a Move/Rename, then these statements are filled in with the new filename. If the file operation is not a Move/Rename, then they will have the same value as the FILE_PATH_xxx statements above.
- FILE_RENAME_DEST_EXTENSION
- File extension of the rename/move destination file, including the dot, such as .TXT. If not a rename/move operation, this will be the same value as FILE_EXTENSION.
Example: (FILE_RENAME_DEST_EXTENSION = ".docx")
- FILE_RENAME_DEST_PATH
- In the case of a rename/move operation, this is the full path to the destination file. If not a rename/move operation, it is the same as FILE_PATH.
Example: (FILE_RENAME_DEST_PATH = "D:\My-Backup-Files\Secret.docx")
- FILE_RENAME_DEST_PATH_IN_CLOUD_FOLDER
- In the case of a rename/move operation, boolean indicating if the rename/move destination path is in a cloud synchronization folder, such as OneDrive, DropBox or GoogleDrive. If not a move/rename operation it is the same as FILE_PATH_IN_CLOUD_FOLDER.
Example: (FILE_RENAME_DEST_PATH_IN_CLOUD_FOLDER = True)
- FILE_RENAME_DEST_PATH_IN_EXTERNAL_DRIVE
- Evaluates to True or False, and will be True if FILE_RENAME_DEST_PATH is on an external drive, such as a USB thumb drive. If not a move/rename operation it is the same as FILE_PATH_IN_EXTERNAL_DRIVE.
Example: (FILE_RENAME_DEST_PATH_IN_EXTERNAL_DRIVE = False)
- FILE_SHA256
- Evaluates to a string consisting of the SHA256 hash of the file. This can potentially be an expensive operation as it requires opening and reading the entire file to compute the hash.
Example: (FILE_SHA256 = "588A31053B19A3E8F5B4E7EF16AC9C45862EB097E9403739B59E0FD437D623EA")
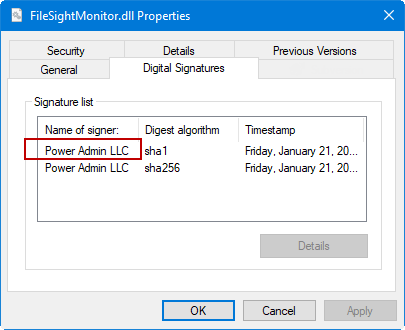
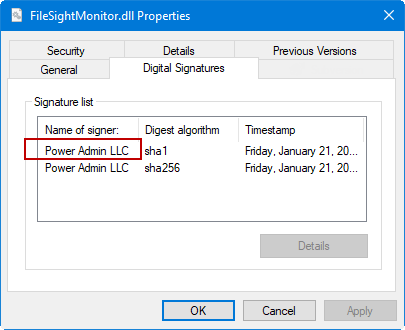
- FILE_SIGNED_BY
- Evaluates to a value extracted from the file's digital signature. If there is no digital signature the value will be an empty string.
Example: (FILE_SIGNED_BY = "Power Admin LLC") OR (FILE_SIGNED_BY = "")
- FILE_SIGNED_BY_TRUSTED
- Evaluates to True or False. The file's digital signature signer is extracted (see FILE_SIGNED_BY) and that value is searched for in the Trusted Publishers list.
If found, the statement evalutes to True. Example: (FILE_SIGNED_BY_TRUSTED = True)
- HOST_NAME
- Evaluates to a string containing the hostname where the rule is being run. This can be the Central Server, a Satellite Server or an Endpoint. Example: (HOSTNAME = "MSDC1")
- PROCESS_IS_COMMAND_HOST
- Evaluates to True or False. The current process name (without the path) that is reading the file being checked is compared to the Command Host list.
If it is found in the list, the statement evaluates to True. Example: (PROCESS_IS_COMMAND_HOST = True)
- PROCESS_IS_SIGNED
- Evaluates to True or False. Indicates whether the executable file, of the process that is accessing the file, contains a digital signature. Example: (PROCESS_IS_SIGNED = False)
- PROCESS_IS_TRUSTED_APP
- Evaluates to True or False. The process' path is compared against entries in the Trusted Applications list and evaluates to True if a match is found, and details about
the file (signer, date, size) also match what was added to the list.
Example: (PROCESS_IS_TRUSTED = True)
- PROCESS_PATH
- Evaluates to a string consisting of the process' executable file path, without any command line arguments. Example: (PROCESS_PATH = "C:\Windows\Notepad.exe")
- PROCESS_PATH_IN_CLOUD_FOLDER
- Evaluates to True or False, and is True if the process is running from within a local cloud folder (OneDrive, Google Drive or DropBox). Example: (PROCESS_PATH_IN_CLOUD_FOLDER = false)
- PROCESS_SHA256
- Evaluates to a string containing the SHA256 hash of the process' executable file. This can be expensive to compute as it requires opening and reading the entire process executable file.
Example: (PROCESS_SHA256 = "A9E8AD0792B546A4A8CE49EDA82B327AD9581141312EFEC3AC6F2D3AD5A05F17")
- PROCESS_SIGNED_BY
- Evaluates to a string containing the process executable file's digital signature signer, or an empty string if there is no digital signature. Example: (PROCESS_SIGNED_BY = "Microsoft Windows")
- PROCESS_SIGNED_BY_TRUSTED
- Evaluates to True or False. The process file's digital signature signer is extracted and then checked against the Trusted Publishers list. If found the
statement evaluates to True. Be cautious with this since most Command Host processes (like cmd.exe and powershell.exe) are signed by a trusted company.
Example: (PROCESS_SIGNED_BY_TRUSTED = True)
- REQUESTOR_HAS_ENDPOINT
- Boolean value indicating whether the file being requested is from a system with one of the following running: the Endpoint, the Central Server or a Satellite server. This statement is only evaluated on the Central Server or a Satellite - it always True when checked on the Endpoint.
Example: (REQUESTOR_HAS_ENDPOINT = True)
- REQUEST_FROM_NETWORK
- Boolean value indicating if the file is being requested from something on the network (i.e. not a local file access). This value is meant to be processed on the server, so the Endpoint always sets it to True.
Example: (REQUEST_FROM_NETWORK = True)
- REQUEST_IPADDRESS
- String value indicating the IP address of the requestor if the request comes from the network. It could potentially hold a local address for requests from the local system. It is mostly used for logging and diagnostics.
- USER_GROUPS
- Evalulates to a comma separated list of all the groups (local and Active Directory) that the user requesting the file read is a member of. Because some group names might contain other group names ("Administrators" could be a substring of "Domain Administrators") it is best to do comparisons with a comma at the start and end of the target group being checked for. Also, wildcards will be needed to ignore the rest of the string in a comparison. In this example, the user is being checked to see if they are part of the local Administrators group:
(USER_GROUPS = "*,Administrators,*")
Comparing against "*Administrators*" could match against Administrators, Domain Administrators, Print Administrators or even HRAdministrators.
- USER_IS_FULL_ACCESS
- This evaluates to True or False depending on if the user (USER_NAME value) is found in the Full Access Users list. Example: (USER_IS_FULL_ACCESS = True)
- USER_NAME
- Evaluates to a string of the logged in user, using domain\username format. Example: (USER_NAME = "OFFICE\Bob")
Learn about Trusted Application Rules next.