This help page is for version 4.0. The latest available help is for version 9.4.
HOWTO - Audit Windows Logons and Logon Failures
When a user logs into a Windows computer, or fails to logon, an event can be written to the Windows Event Log. This feature is built in to Windows.
The Event Log monitor in PA Server Monitor can tell you when one of these events occurs, thus alerting you to a server logon, or a failed server logon. And because the Event Log monitor has a configurable monitoring cycle (the Schedule button in the lower right corner), you can find out about the logon in nearly real time.
Create the Event Log monitor
- Create an Event Log monitor on the server that you want to check. It's OK if there is already an existing Event Log monitor on the server -- you can have multiple monitors of any type on a server, or you can combine the steps below into your existing Event Log monitor.
- Ensure the "Security" Event Log in the lower left corner is checked
- In the large grid, go to the "Security" source (for Windows 2003 servers) or the "Microsoft Windows security auditing" source (for Windows 2008 or newer) and check the Audit Success and Audit Failure boxes. If both sources are available, check both (that way you'll be able to copy this monitor to other computers and it will work for both 2003 and 2008 servers).
- In the source line(s) above, click the box in the first column labeled Filters. We're going to set a filter for the following Event IDs:
- 528 - Successful Logon
- 529 - Logon Failure: Unknown user name or bad password
- 530 - Logon Failure: Account logon time restriction violation
- 531 - Logon Failure: Account currently disabled
- 532 - Logon Failure: The specified user account has expired
- 533 - Logon Failure: User not allowed to logon at this computer
- 534 - Logon Failure: The user has not been granted the requested logon type at this machine
- 535 - Logon Failure: The specified account's password has expired
- 537 - Logon Failure: An unexpected error occurred during logon
- 539 - Logon Failure: Account locked out
- 540 - Successful network logon
- 644 - User Account Locked Out
- 4624 - An account was successfully logged on
- 4625 - An account failed to log on
- 4649 - A replay attack was detected
- 4740 - A user account was locked out
- 5378 - The requested credentials delegation was disallowed by policy
See http://support.microsoft.com/kb/947226
To add the filter, add the following to the "Included Event IDs and event text" field:
528-535,537,539,540,644,4624,4625,4649,4740,5378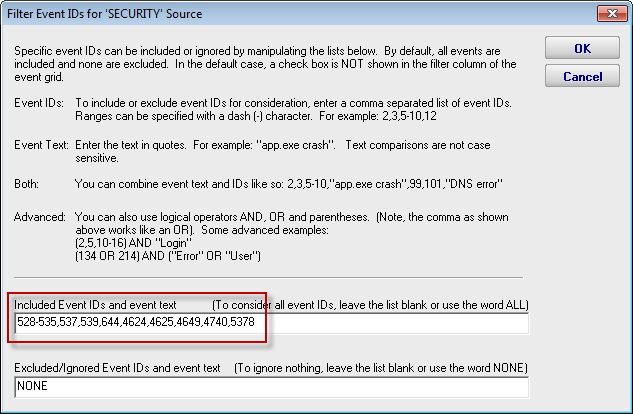
You can adjust the list of Event IDs that are being filtered, and add additional filters for watching for particular text (like a specific username for example). To do that, just add more to the filter line.
For example, to alert on a logon success or failure by account "watch_me", set the filter line to:
(528-535,537,539,540,644,4624,4625,4649,4740,5378) AND ("watch_me")
Now this Event Log monitor will alert on logons and failed logons to the server that it's monitoring. Add actions (the Email Action for example) to specify how you want to be alerted.
References:
http://blogs.msdn.com/b/ericfitz/archive/2004/12/09/279282.aspx
http://blogs.msdn.com/b/ericfitz/archive/2007/05/08/the-trouble-with-logoff-events.aspx
http://blogs.msdn.com/b/ericfitz/archive/2008/08/20/tracking-user-logon-activity-using-logon-events.aspx
http://blogs.msdn.com/b/ericfitz/archive/2009/06/10/mapping-pre-vista-security-event-ids-to-security-event-ids-in-vista.aspx
http://support.microsoft.com/default.aspx?scid=kb;EN-US;947226
http://www.microsoft.com/download/en/details.aspx?DisplayLang=en&id=17871
http://www.microsoft.com/download/en/details.aspx?displaylang=en&id=21561
http://www.ultimatewindowssecurity.com/securitylog/encyclopedia/Default.aspx